Around October of 2021 I was running out of disk space on my 6TB hard drive that I had acquired back on November 2015, so I decided to upgrade to the newest and greatest storage solutions of all time: 14TB of block storage! I went ahead and purchased a WD Elements 14TB USB 3.0 external hard drive, proceeded to format it down and get it ready for storing all my useful content.
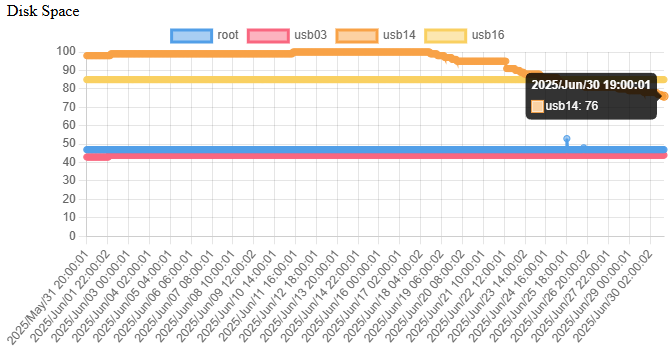
From October 2021 to July 2025 I completely filled that volume up, and just recently hit the 100% usage. What to do? By the looks of the graph I figured that out without having to delete any files…